Agentic Investigation
AI personas autonomously triage, enrich, and resolve alerts across 250+ tools — applying organizational context, asset criticality, and live threat intel on every decision.
The agentic AI SecOps platform for the modern enterprise.
An agentic XDR platform that fuses endpoint, identity, cloud, network, and SaaS telemetry — then puts AI personas to work alongside named human analysts to detect, investigate, contain, and resolve threats at machine speed, 24/7/365.
Legacy MDRs are alert factories. They tune for the average customer, ignore your business context, and drown your team in low-fidelity noise while attackers exfiltrate data in under 6 minutes. Static playbooks, siloed tools, and the global SOC analyst shortage leave most enterprises with 200+ day dwell times and no real path to outpace AI-enabled adversaries.
Eliminate blind spots and reduce noise through a unique combination of timely, curated intelligence, operationalized by AI, and put to work by expert human partnership.
Specialized AI personas — not single-task bots — autonomously investigate 100% of alerts, run hypothesis-driven hunts, build detections from natural language, and generate tailored threat intel. Outcomes, not chores.
We unify EDR, SIEM, NDR, identity, email, cloud, and SaaS telemetry into one correlated picture — across 250+ technologies — so detection happens at the source and response happens everywhere at once.
Every agentic action is shaped by certified Maverc analysts with continuous QA, guardrails, and feedback loops. AI moves at machine speed; humans own accountability and trust.
Our AI synthesizes patterns from detections, hunts, investigations, and live threat intel to forecast likely attacks against your environment — and recommends proactive action before adversaries strike.
Maverc Agentic XDR is built for a world where attackers breach in 4 minutes. We unify your entire security stack into one open XDR fabric and deploy specialized agentic AI teammates — an Investigation & Response Analyst, Detection Engineer, Threat Hunter, and Threat Intel Analyst — that reason across alerts, hunts, and intel to drive defined outcomes, not just close tickets. Every action is governed by certified human responders who own your environment end-to-end.
Engineered components delivered as a unified, outcome-driven platform.
Real views from the Maverc detection & response platform — the same console our analysts use to hunt, triage, and respond on your behalf 24/7.
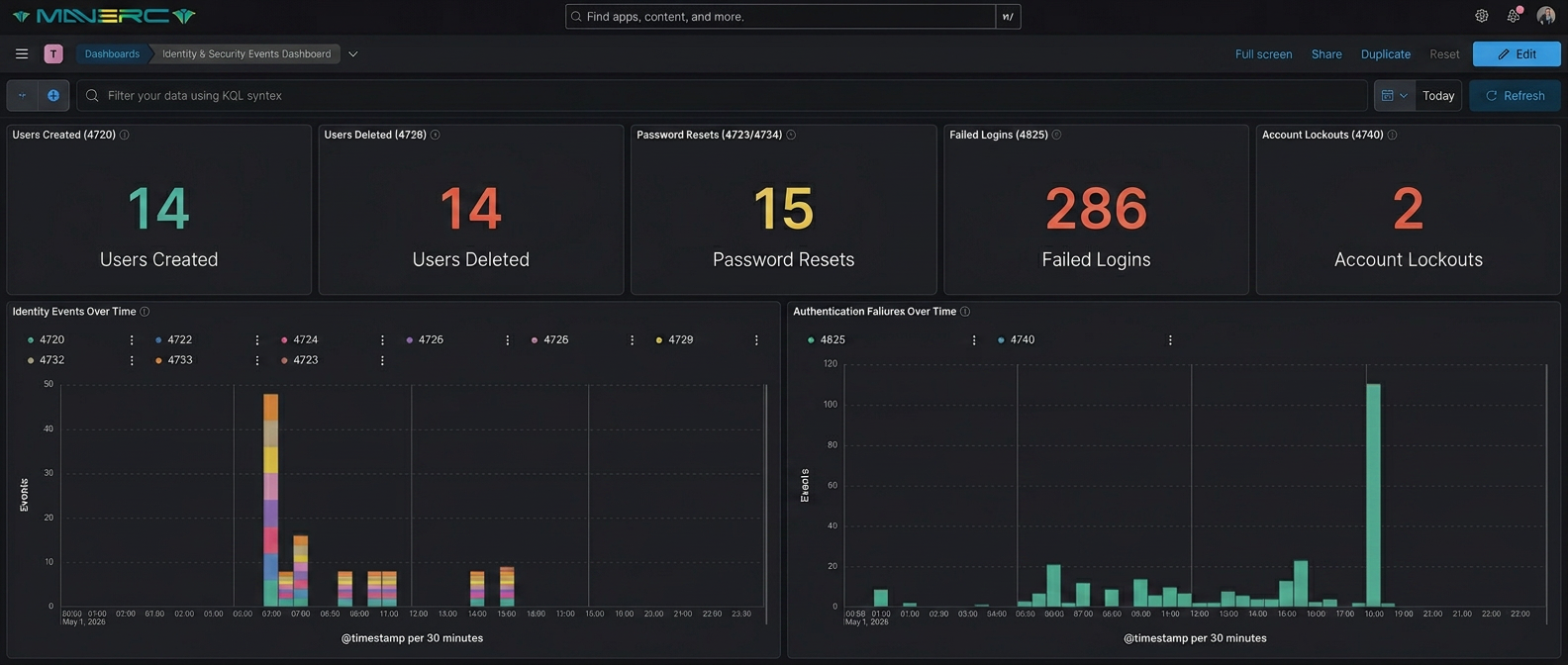
Unified identity, endpoint, and authentication telemetry — investigated and triaged autonomously by Maverc agentic personas.
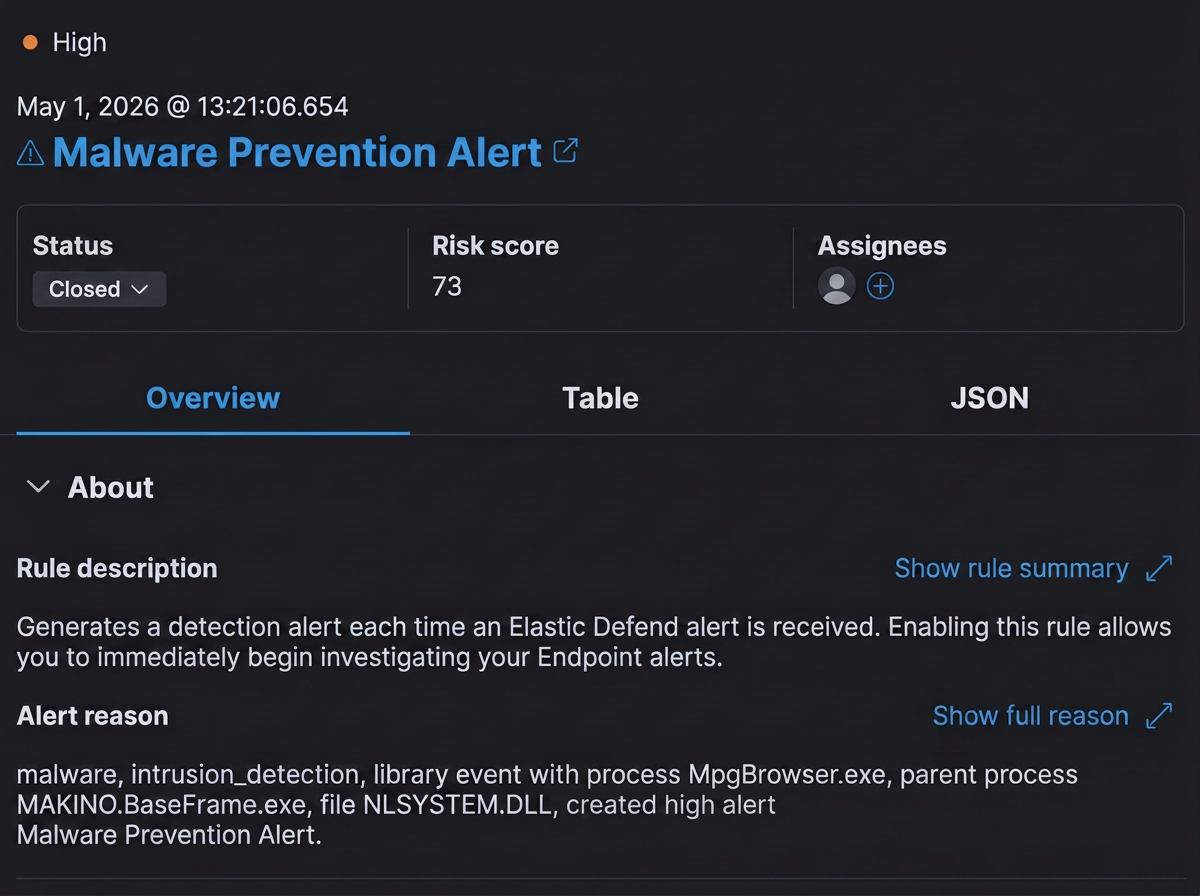
Risk-scored alert auto-enriched, contextualized, and resolved by the IR Analyst persona — closed in minutes, not hours.

Process-tree timelines stitched across hosts so the Threat Hunter persona can pivot from a single signal to the full kill chain.
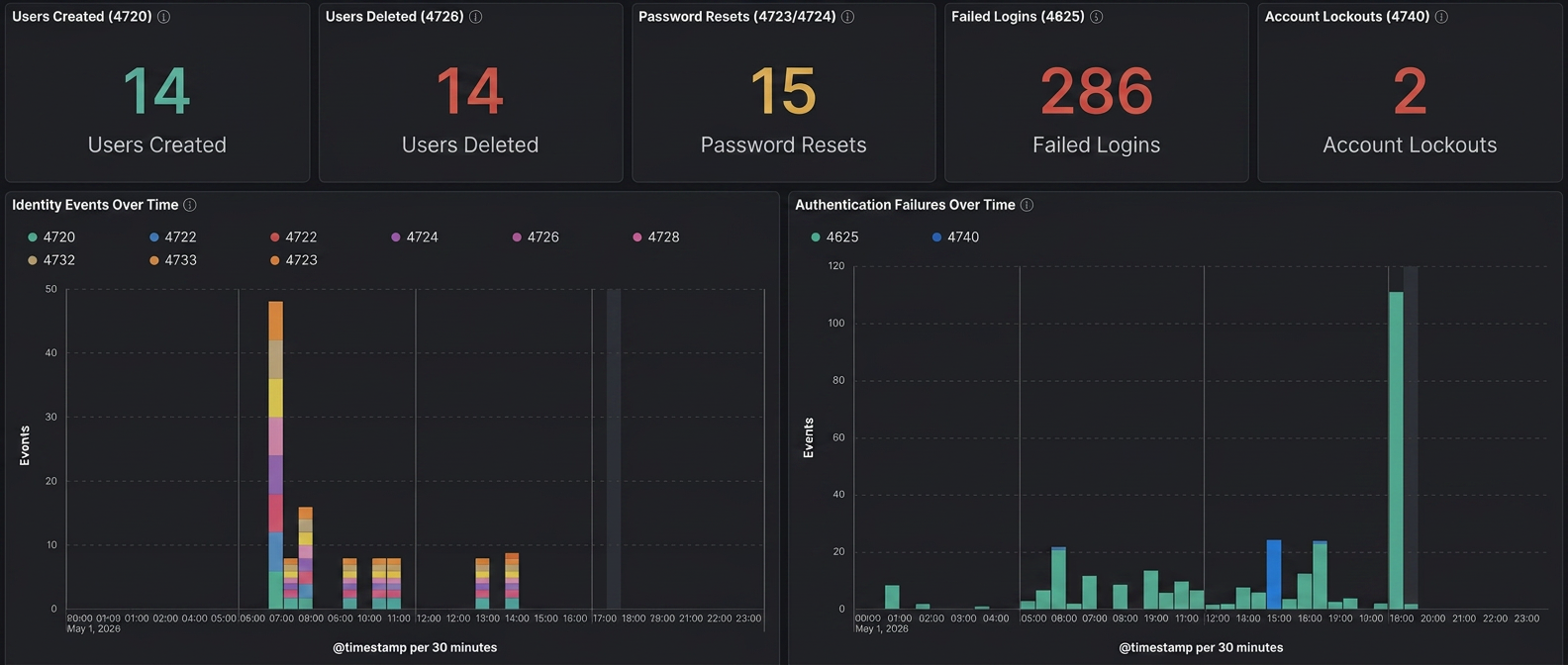
Real-time visibility into account creation, lockouts, failed logins, and identity attack patterns across your workforce.
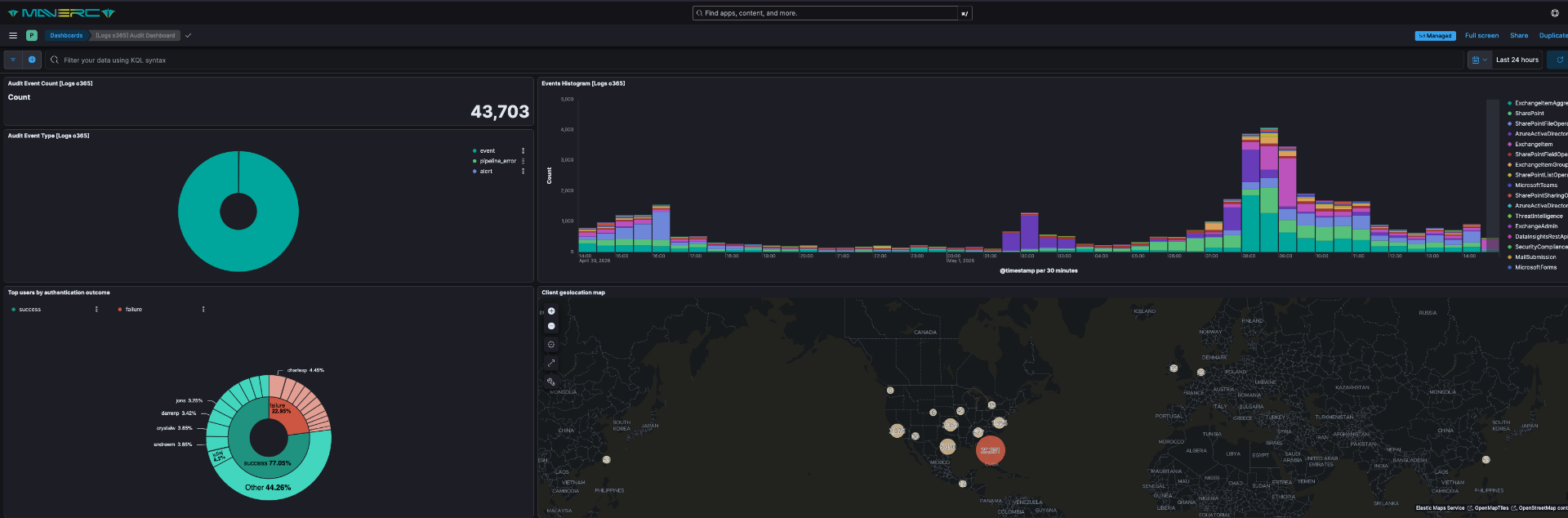
Worldwide sign-in map surfaces impossible-travel, anomalous access, and identity compromise the moment it happens.
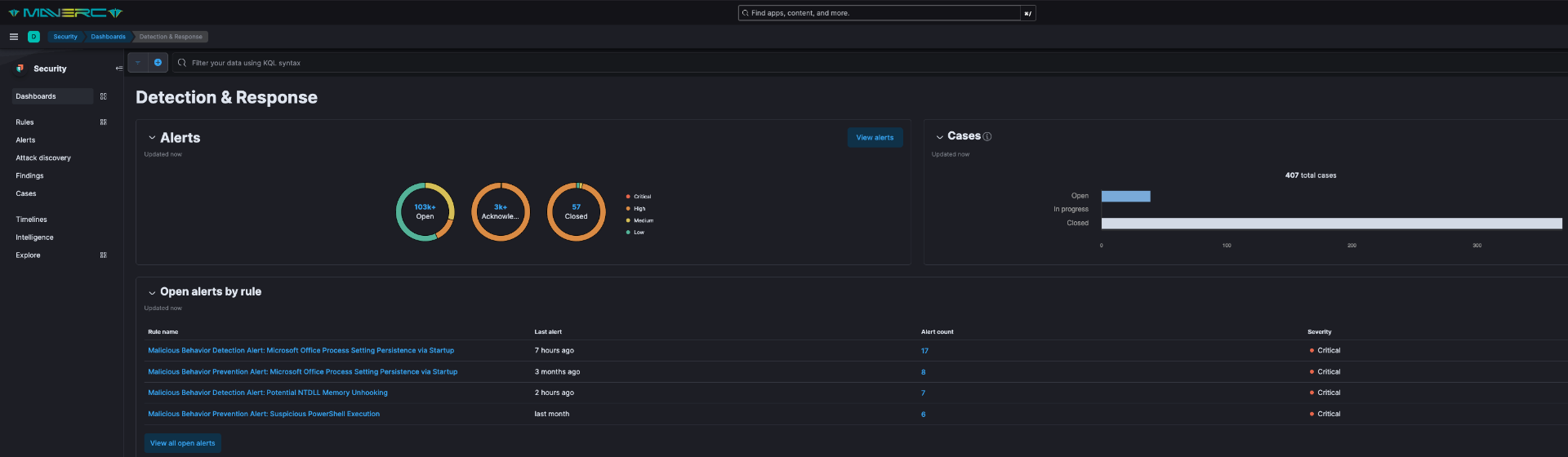
The Detection Engineer persona builds, tunes, and deploys analytics across your stack from natural-language input.
AI personas autonomously triage, enrich, and resolve alerts across 250+ tools — applying organizational context, asset criticality, and live threat intel on every decision.
Launch hypothesis-driven hunts across your entire stack from a chat window. Pre-built hunt packages plus custom queries — analyzed and reported automatically.
Build, test, and deploy detection logic in any technology with natural-language input. Coverage gap analysis runs continuously against MITRE ATT&CK.
Statistical analysis of detections, hunts, and external intel forecasts likely attacks against your environment — and recommends proactive action.
Full-scale, AI-powered protection delivered by one trusted partner — combining expert analysts, deep threat intelligence, and continuous coverage across your entire environment.
30-day onboarding with telemetry validation, detection baseline, runbook authoring, and crown-jewel scoping.
Multi-source correlation across endpoint, network, identity, cloud, SaaS, and curated threat intel.
Triage in minutes, contain with pre-authorized actions, eradicate with full forensics and root-cause analysis.
Every incident feeds back into detection logic, hunt hypotheses, and your defensive posture.
Three engagement models — from advanced threat hunting to a fully managed elite partnership with incident readiness baked in.
Advanced proactive hunting layered on your existing controls.
Core 24/7 detection, response, and triage for modern enterprises.
Full-spectrum defense with named advisors and IR retainer included.
MSS Elite customers can layer on a breach response warranty of up to $1M in case a major breach goes undetected — providing financial relief when it matters most.
Yes. You get a named pod — a lead analyst, deputy, and detection engineer — who learn your environment and stay with your account.
No. Maverc MSS is platform-agnostic and integrates with what you already own. If your stack has gaps, we'll recommend — never force — alternatives.
Pre-negotiated DFIR hours, breach exercises, compromise assessments, IR plan reviews, and on-demand access to senior responders during an active incident.
P1 acknowledged within 5 minutes, contained within 30. SLAs are contractual with service credits for any miss.
Available as an add-on to MSS Elite. Coverage scales with your endpoint count and is underwritten by our cyber-insurance partners.
Send us a few details and a Maverc advisor will follow up within one business day with a tailored conversation.